SOCKS5 vs HTTP Proxies
When to reach for SOCKS5 and when an HTTP proxy is the better tool.
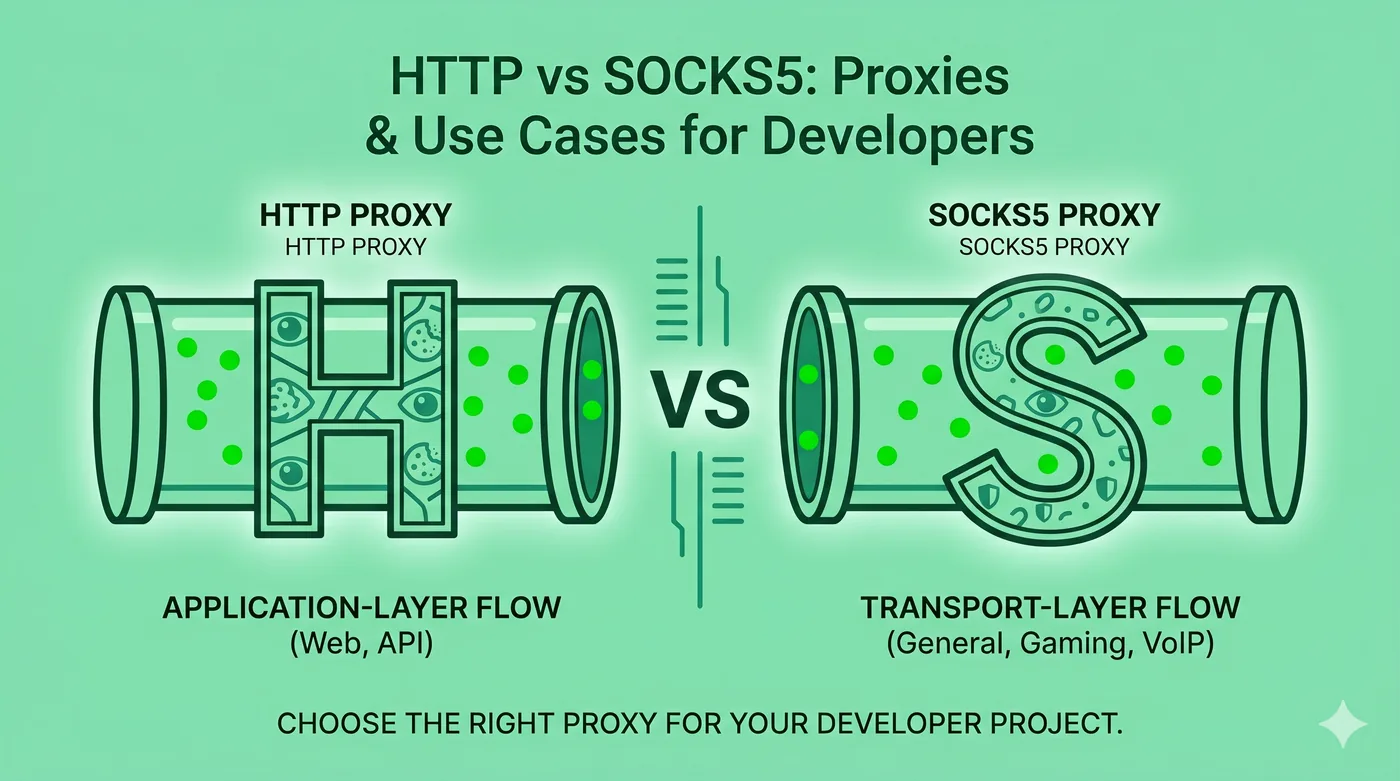
HTTP proxies understand web traffic and can inspect or modify it; SOCKS5 proxies are transport-layer relays that can carry any TCP or UDP traffic. Use HTTP proxies for caching and filtering web traffic; use SOCKS5 when you need to proxy non-web protocols like SSH, IRC, or game traffic.
Key takeaways
- HTTP proxies operate at OSI layer 7 — they understand requests and responses.
- SOCKS5 operates at layer 5 — it’s protocol-agnostic.
- SOCKS5 is the right choice for SSH, BitTorrent, or game traffic.
- Neither protocol encrypts by default; tunnel them inside SSH or TLS for safety.
HTTP proxies in detail
An HTTP proxy reads the HTTP headers of every request that passes through it. That means it can cache responses, log URLs, filter content, and modify headers. It’s the right tool when you only care about HTTP/HTTPS.
SOCKS5 in detail
SOCKS5 doesn’t care what’s inside the packets it relays. It supports TCP and UDP, IPv6, and username/password authentication. Because it doesn’t parse traffic, it’s lightweight — but it also can’t cache or filter at the application layer.
Real-world examples
Web scraping behind a corporate firewall — HTTP proxy. Forwarding game traffic — SOCKS5. SSH bastion access through a jump host — SOCKS5. Filtering inappropriate websites in a school — HTTP proxy.
Adding encryption
Both protocols pass traffic in the clear by default. For privacy, tunnel SOCKS5 inside an SSH session (`ssh -D`) or use HTTPS-only HTTP proxies with authentication.
Frequently asked questions
Is SOCKS5 the same as a VPN?
No. SOCKS5 only routes traffic for apps configured to use it. A VPN routes traffic for the entire device.
Can SOCKS5 proxy my whole computer?
Not without a helper that captures all traffic. A VPN is the simpler option for full-device coverage.
Which is faster?
Usually SOCKS5, because it doesn’t inspect or rewrite traffic.
Related guides
Forward Proxy vs Reverse Proxy: What’s the Difference?
Same word, two completely different jobs. Here’s a clean mental model.
Read article →Residential vs Datacenter Proxies: Honest Comparison
What each one is, what they’re actually used for, and the ethical lines that matter.
Read article →How Businesses Use Proxies for Legitimate Web Data Collection
Price comparison, SEO, brand protection — and how to do it without breaking rules.
Read article →