Proxy Server Setup for a Small Business Network
A practical, vendor-neutral walkthrough using widely available open-source tools.
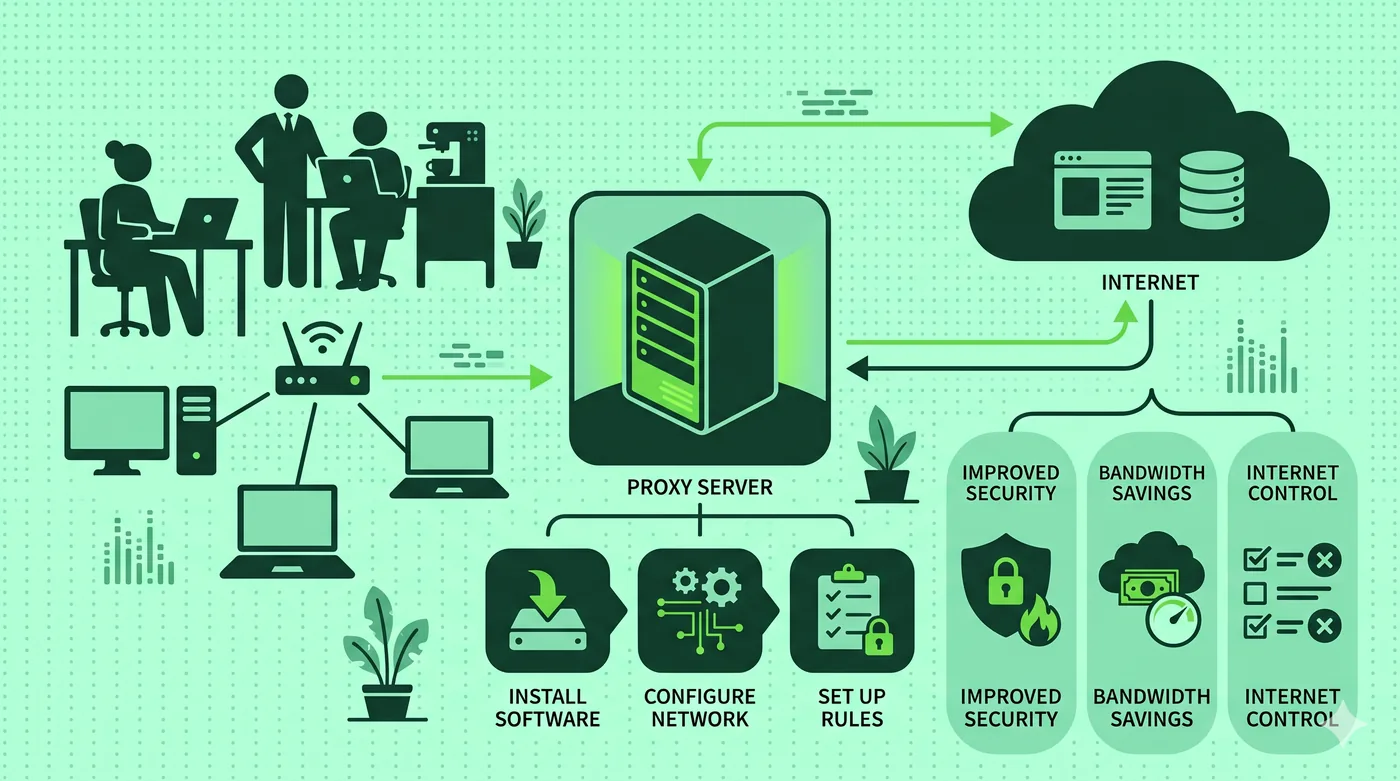
A small business proxy server filters and caches outbound web traffic for the office. Squid on a small Linux server is the most common open-source choice — install it, configure ACLs based on your IP range, and point devices at it via DHCP option 252 or a PAC file.
Key takeaways
- Squid is the de-facto open-source forward proxy for small offices.
- Use access-control lists to restrict who can use the proxy.
- Cache static assets to save bandwidth on shared connections.
- Audit logs need a written retention policy before you collect them.
Pick the host
A modest Linux VM with 2 vCPU and 4 GB RAM handles dozens of concurrent users comfortably. Use an LTS distribution and disable unused services. Place the VM on a subnet that all clients can reach.
Install and harden Squid
Install Squid via your distro’s package manager. Restrict the listening interface to your internal network. Add an ACL that limits clients to your office IP ranges. Disable HTTP CONNECT to ports you don’t use.
Distribute the configuration
The cleanest method is a PAC file served from your internal web server, distributed via DHCP option 252 or browser policies. Devices auto-configure with no manual steps.
Logging — and what not to log
Squid can log every URL. That is powerful and risky. Decide in writing how long logs are kept, who can access them, and whether employees are informed. A short retention window is usually enough.
Frequently asked questions
Do I need to inspect HTTPS?
Inspecting HTTPS requires installing a custom root certificate on every device — a major step. Most small offices don’t need it; logging the destination hostnames is enough.
Is a proxy a firewall?
No. A proxy filters specific protocols. A firewall sits at the perimeter and enforces network policy. Use both.
How do I monitor performance?
Squid exposes metrics; tools like Grafana/Prometheus or simple log analysis tell you cache hit rates and slow upstreams.
Related guides
Forward Proxy vs Reverse Proxy: What’s the Difference?
Same word, two completely different jobs. Here’s a clean mental model.
Read article →Residential vs Datacenter Proxies: Honest Comparison
What each one is, what they’re actually used for, and the ethical lines that matter.
Read article →SOCKS5 vs HTTP Proxies: Use Cases for Developers
When to reach for SOCKS5 and when an HTTP proxy is the better tool.
Read article →