Encrypted Messaging Apps Compared
Signal, WhatsApp, iMessage, Telegram — what they actually encrypt, and from whom.
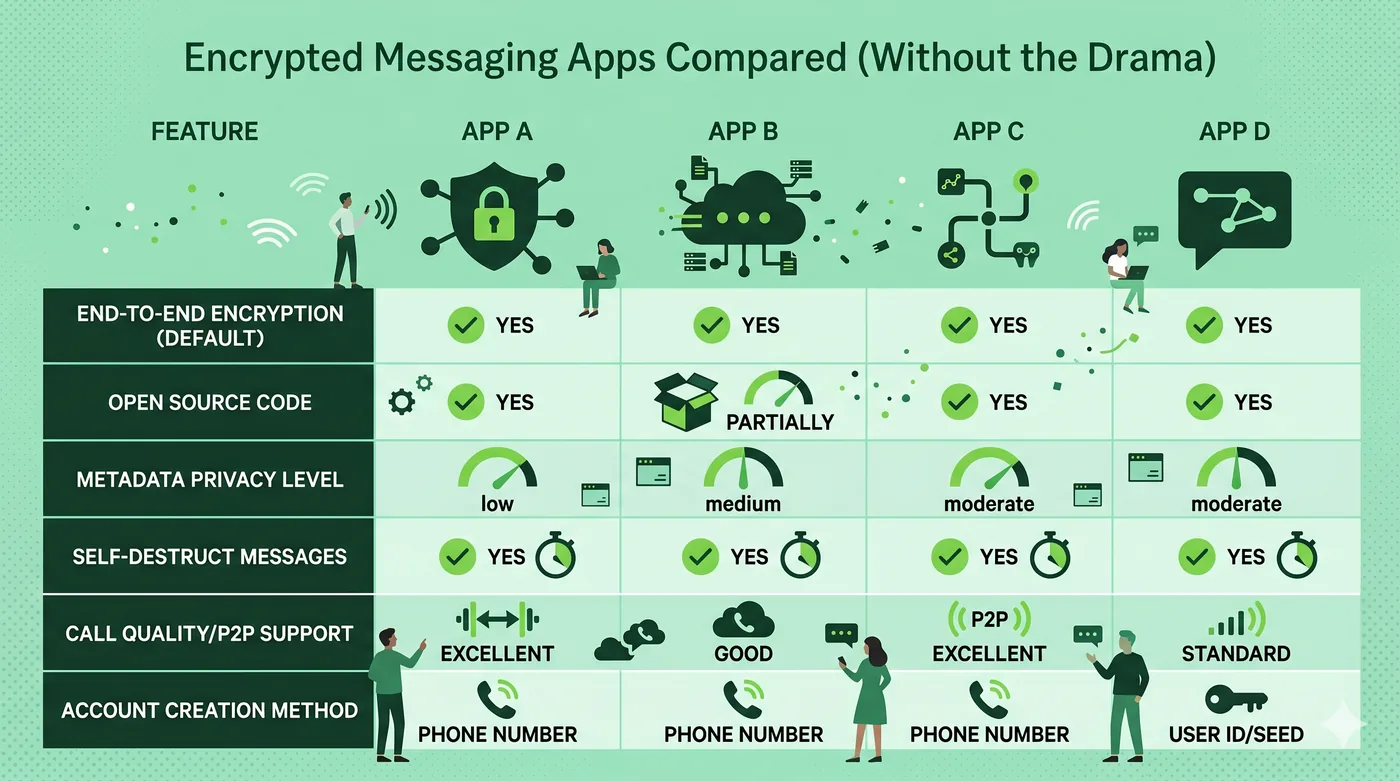
Signal, WhatsApp, and iMessage all use end-to-end encryption for messages by default. Telegram’s standard chats are not end-to-end encrypted — only ‘Secret Chats’ are. The differences come down to metadata, group features, and who runs the servers.
Key takeaways
- End-to-end encryption means servers can’t read message content.
- Telegram regular chats are not end-to-end encrypted — Secret Chats are.
- Metadata (who messaged whom, when) is harder to hide than message text.
- Signal collects the least metadata of the major apps.
Signal
Open-source, non-profit, designed from the ground up to minimise metadata. Phone-number-based registration; usernames now also supported. The default for privacy-conscious users.
Uses the same Signal Protocol for message content. Owned by Meta, which means metadata may be shared with related products. Best when most of your contacts already use it.
iMessage
End-to-end encrypted between Apple devices. SMS fallback to non-Apple users is not encrypted (though RCS support is improving this). iCloud backup, if enabled with the default key, can weaken the protection — turn on Advanced Data Protection for stronger guarantees.
Telegram
Cloud Chats — the default — are encrypted in transit but not end-to-end; Telegram’s servers can read them. ‘Secret Chats’ are end-to-end but device-specific. Don’t assume Telegram is private unless you’re explicitly using Secret Chats.
Frequently asked questions
Which is best for journalists or activists?
Signal is the consensus answer — minimal metadata, audited, non-profit governance.
Are deleted messages really gone?
From your devices and the recipient’s devices, yes. Server-side, depends on the provider’s retention.
Is end-to-end encryption legal everywhere?
It’s under political pressure in several countries. Use the apps available where you live and travel.
Related guides
Browser Privacy Settings: A Quick Tune-Up Guide
Ten minutes in your browser settings cuts the majority of casual tracking.
Read article →Cookies, Trackers, and Fingerprinting Explained
Three different ways the web identifies you — and why blocking only one isn’t enough.
Read article →DNS Privacy Explained: DoH, DoT, and Why They Matter
Every website you visit starts with a DNS lookup. By default, that lookup is unencrypted.
Read article →