Encrypted Messengers Compared
Default end-to-end encryption, metadata, multi-device, and account requirements.
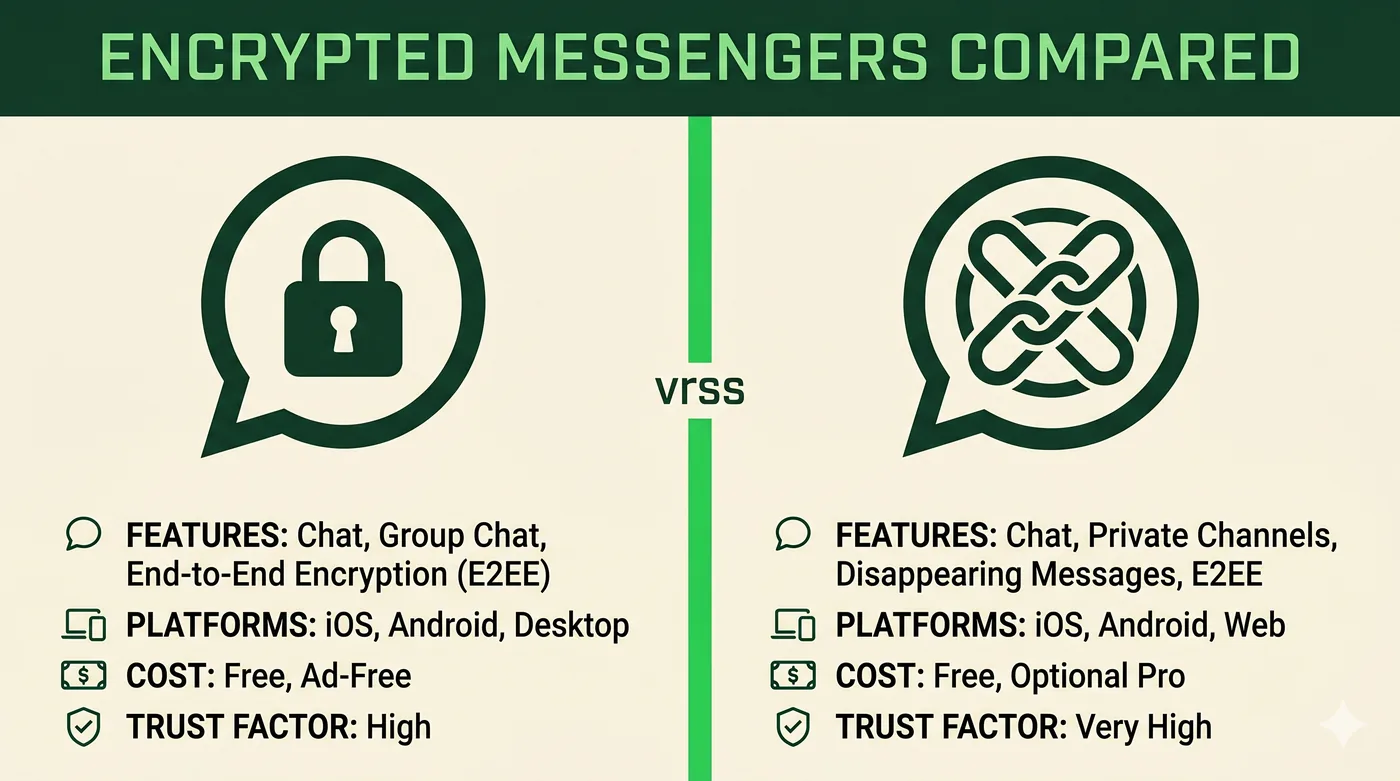
For most readers, Signal is the simplest E2EE-by-default choice. iMessage is fine inside Apple's ecosystem. WhatsApp is E2EE for content but collects the most metadata. Matrix and Session offer different trade-offs around federation and metadata avoidance.
All major messengers now offer some form of end-to-end encryption (E2EE), but the defaults and metadata stories differ. We focus on technical properties available from public documentation; check each app's current docs before relying on a specific behavior.
| Signal | iMessage | Matrix (Element) | Session | ||
|---|---|---|---|---|---|
| E2EE by default | Yes | Yes (Apple-to-Apple) | Yes | Yes (in supporting clients) | Yes |
| Account requirement | Phone number | Apple ID | Phone number | Email or username | None (random ID) |
| Open-source clients | Yes | No | Partial | Yes | Yes |
| Open-source server | Yes | No | No | Yes (federated) | Yes |
| Multi-device | Yes (linked devices) | Yes (Apple devices) | Yes (linked devices) | Yes | Limited |
| Metadata minimization | Strong | Moderate | Weakest of the five | Depends on home server | Strong (onion routing) |
| Disappearing messages | Yes | Yes (recent versions) | Yes | Yes | Yes |
| Best for | Default secure messenger | Friends and family inside Apple | Reaching the largest user base safely | Federation-friendly orgs and communities | Avoiding identifiers entirely |
Frequently asked questions
Is iMessage really end-to-end encrypted?
Yes between Apple devices, with optional Advanced Data Protection extending it to backups. SMS fallback (or RCS without E2EE) is not E2EE.
Why does WhatsApp score lower on metadata?
Because it shares some metadata with its parent company by default, and ties accounts to phone numbers. Content remains encrypted; the question is who knows you talked to whom and when.
Is Session worth using?
If avoiding any identifier is your goal, yes. If you want to reach mainstream contacts, no — the network is much smaller.
Go deeper
Other comparisons
VPN vs Proxy vs Tor
Three tools people lump together — what each one actually does, and when to reach for which.
Compare2FA Methods Compared
SMS, email, TOTP, push and hardware keys — security, convenience and recovery.
ComparePassword Manager Categories
Browser built-in, cloud-synced, local-only, and self-hosted — strengths and trade-offs.
CompareVPN vs Proxy
Two tools commonly confused — picking the right one starts with knowing what each guarantees.
CompareHTTP Proxy vs SOCKS5 Proxy
Web-only convenience versus protocol-agnostic flexibility — which to use, and when.
CompareResidential Proxy vs Datacenter Proxy
Same idea, very different IPs — and very different prices and detection profiles.
CompareGoogle Drive vs OneDrive
Two consumer cloud services whose strengths track the suite around them.
CompareDropbox vs Google Drive
Sync engine and sharing versus integrated suite — different strengths.
CompareWordPress vs Wix
Open-source flexibility versus all-in-one hosted simplicity.
CompareFramer vs Webflow
Two visual builders aimed at design-led teams — different sweet spots.
CompareChatGPT vs Gemini
Two of the most-used AI assistants — different ecosystems, similar fundamentals.
CompareClaude vs ChatGPT
Two leading assistants with different defaults — and different strengths.
CompareCanva vs Adobe Express
Two template-driven design tools competing for the non-designer.
CompareNotion vs Google Docs
A flexible-blocks workspace versus a real-time word processor.
CompareShared Hosting vs VPS
Cheapest start versus a slice of a server with full control.
CompareCloud Hosting vs Shared Hosting
Elastic, pay-per-use compute versus fixed shared servers.