2FA Methods Compared
SMS, email, TOTP, push and hardware keys — security, convenience and recovery.
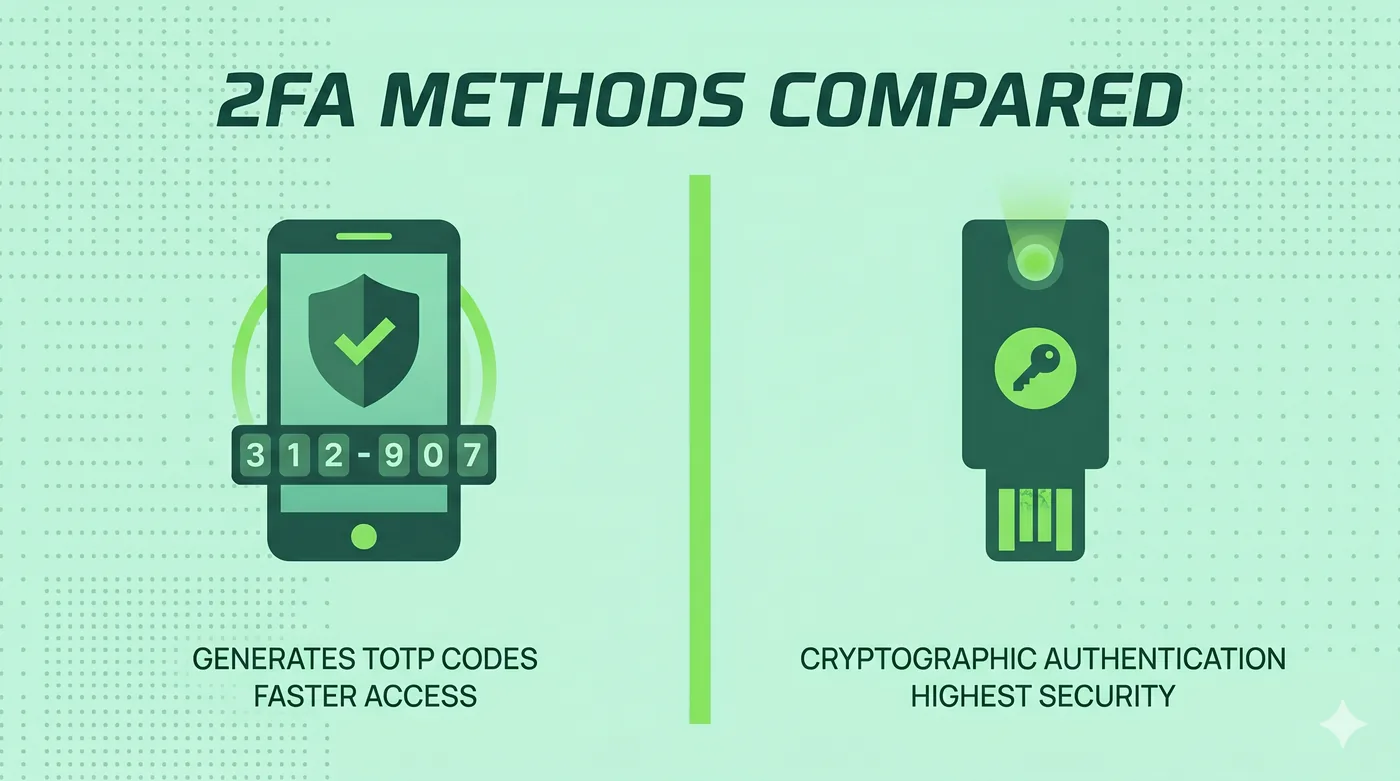
For best security, use a hardware key (FIDO2/WebAuthn) where supported, with TOTP as a fallback. Avoid SMS for high-value accounts because of SIM-swap risk.
Any 2FA is better than no 2FA, but the methods differ wildly in how phishable, interceptable and recoverable they are. The further down the table, the stronger the method.
| SMS code | Email code | TOTP app | Push approval | Hardware key (FIDO2) | |
|---|---|---|---|---|---|
| Phishing-resistant | No | No | No | Partial | Yes |
| Resistant to SIM-swap | No | Yes | Yes | Yes | Yes |
| Works offline | No (needs cell) | No | Yes | Partial (cached) | Yes |
| Setup difficulty | None | None | Low (scan QR) | Low | Moderate (buy + register) |
| Recovery if device lost | Reissue SIM | Email recovery | Backup codes / sync | Backup codes / second device | Spare key (you should own two) |
| Cost | Free | Free | Free | Free | $25–$80 per key |
| Best for | Last-resort fallback | Low-value accounts | Most personal accounts | Convenience on managed mobile | Email, password manager, identity provider, dev tooling |
Frequently asked questions
Should I always buy two hardware keys?
Yes. One stays with you; one stays in a safe. Replacing a single lost key without a backup is a slow and painful process.
Is push 2FA safe?
It's safer than SMS but vulnerable to MFA-fatigue prompts. Use number-matching where the service supports it.
Can I mix methods?
Yes — and you should. Hardware key as primary, TOTP as backup, recovery codes printed out.
Go deeper
Other comparisons
VPN vs Proxy vs Tor
Three tools people lump together — what each one actually does, and when to reach for which.
ComparePassword Manager Categories
Browser built-in, cloud-synced, local-only, and self-hosted — strengths and trade-offs.
CompareEncrypted Messengers Compared
Default end-to-end encryption, metadata, multi-device, and account requirements.
CompareVPN vs Proxy
Two tools commonly confused — picking the right one starts with knowing what each guarantees.
CompareHTTP Proxy vs SOCKS5 Proxy
Web-only convenience versus protocol-agnostic flexibility — which to use, and when.
CompareResidential Proxy vs Datacenter Proxy
Same idea, very different IPs — and very different prices and detection profiles.
CompareGoogle Drive vs OneDrive
Two consumer cloud services whose strengths track the suite around them.
CompareDropbox vs Google Drive
Sync engine and sharing versus integrated suite — different strengths.
CompareWordPress vs Wix
Open-source flexibility versus all-in-one hosted simplicity.
CompareFramer vs Webflow
Two visual builders aimed at design-led teams — different sweet spots.
CompareChatGPT vs Gemini
Two of the most-used AI assistants — different ecosystems, similar fundamentals.
CompareClaude vs ChatGPT
Two leading assistants with different defaults — and different strengths.
CompareCanva vs Adobe Express
Two template-driven design tools competing for the non-designer.
CompareNotion vs Google Docs
A flexible-blocks workspace versus a real-time word processor.
CompareShared Hosting vs VPS
Cheapest start versus a slice of a server with full control.
CompareCloud Hosting vs Shared Hosting
Elastic, pay-per-use compute versus fixed shared servers.